Juniper Networks offers a wide range of firewall products
Virtual
For private cloud, hybrid cloud or public cloud environments, their virtual firewalls provide uncompromised flexibility, effectiveness and performance.
Small enterprise and branch office
Whether rolling out new services and applications across locations, connecting to the cloud, or trying to achieve operational efficiency, their branch firewalls helps organisations realise their business objectives.
Mid-size enterprise and data centre
Compact, high-performance, next-generation firewalls with hardware-accelerated security services protect mission-critical people, data and infrastructure.
Large data centre and service providers
Highly effective protection, market-leading performance, reliability and availability ideally suited to service provider, large enterprise, and public sector organizations.
SRX features
Security for any size data center and enterprise edge
- Offers a broad range of options—from all-in-one, integrated physical and virtual security networking devices to highly scalable, chassis-based data centre solutions—that can defend enterprise data centres and service providers of any size.
Maximum performance and scale
- Supports fast, secure, and highly available data centre and enterprise edge operations, with unmatched performance and scalability, massive session volumes, and flexible large-scale connectivity, with ultra-low latency performance of up to 1 Tbps.
Superior security value
- Provides outstanding value for high-speed, highly effective security services—even with multiple services enabled. The system’s flexible, modular approach protects your investment by scaling for future network growth.
Comprehensive threat protection
- Provides advanced, next-generation defence against known and unknown threats, with a comprehensive suite of layered security services both on-premises and in the cloud. All SRX Series gateways are built for resiliency, scalability, and availability to secure data centres or the enterprise edge against the broadest spectrum of threats.
Carrier-grade reliability
- Delivers continuous uptime through in-service hardware and software upgrades, redundant components, and carrier-class hardware for resiliency. The high-end SRX Series gateways deliver six-nine reliability for nonstop business continuity and application availability.
Virtual Security Option
- High-performance network security in a virtual form factor, the vSRX, helps network operators in highly dynamic environments.

Juniper Networks SRX firewalls
Juniper Networks SRX300
Securing small branch or retail offices, the SRX300 Services Gateway consolidates security, routing, switching, and WAN connectivity in a small desktop device. The SRX300 supports up to 1 Gbps firewall and 300 Mbps IPsec VPN in a single, cost-effective networking and security platform.

Juniper Networks SRX firewalls
Juniper Networks SRX320
Securely connecting small distributed enterprise branch offices, the SRX320 Services Gateway consolidates security, routing, switching, and WAN connectivity in a small desktop device. The SRX320 supports up to 1 Gbps firewall and 300 Mbps IPsec VPN in a single, consolidated, cost-effective networking and security platform.

Juniper Networks SRX firewalls
Juniper Networks SRX340
Securely connecting midsize distributed enterprise branch offices, the SRX340 Services Gateway consolidates security, routing, switching, and WAN connectivity in a 1 U form factor. The SRX340 supports up to 3 Gbps firewall and 600 Mbps IPsec VPN in a single, cost-effective networking and security platform.

Juniper Networks SRX firewalls
Juniper Networks SRX345
Best suited for midsize to large distributed enterprise branch offices, the SRX345 Services Gateway consolidates security, routing, switching, and WAN connectivity in a 1 U form factor. The SRX345 supports up to 5 Gbps firewall and 800 Mbps IPsec VPN in a single, consolidated, cost-effective networking and security platform.

Juniper Networks SRX firewalls
Juniper Networks SRX380
A high-performance and secure SD-WAN gateway, the SRX380 offers superior and reliable WAN connectivity while consolidating security, routing, and switching for distributed enterprise offices. The SRX380 features greater port density than other SRX300 models, with 16x1GbE PoE+ and 4x10GbE ports, and includes redundant dual power supplies, all in a 1 U form factor.

Juniper Networks SRX firewalls
Juniper Networks SRX550
The SRX550 Services Gateway is an all-in-one solution that consolidates security, routing, switching, and WAN connectivity into a single 2 U device. It is a robust, highly flexible device for next-generation security, delivering enterprise-class networking for protecting midsized-to-large branch locations and supporting up to 7 Gbps firewall, 1 Gbps IPsec VPN, and 800 Mbps intrusion prevention system (IPS).

Juniper Networks SRX firewalls
Juniper Networks SRX1500
The SRX1500 provides 12 1GbE RJ-45 ports, 4 1GbE SFP ports, and 4 10GbE SFP+ ports, plus 2 Physical Interface Module (PIM) slots for scalable, secure connectivity. Dedicated 1GbE ports are available for out-of-band management, high availability control, and front-to-back airflow.

Juniper Networks SRX firewalls
Juniper Networks SRX4100 - SRX4200
The SRX4000 line includes two models, each of which delivers market-leading performance, scalability, and security services in a compact, 1 U platform:
- The SRX4100 supports up to 20 Gbps Internet mix (IMIX) and 9.5 Gbps next-generation firewall performance.
- The SRX4200 supports up to 40 Gbps IMIX and 19 Gbps next-generation firewall performance.
Both models offer eight 10GbE small form-factor pluggable plus (SFP+) front-panel ports.

Juniper Networks SRX firewalls
Juniper Networks SRX4600
The high-performance SRX4600 next-generation firewall offers fast, scalable protection for enterprise private cloud, campus networks, cloud service providers, and telcos. With integrated malware prevention and a full suite of next-generation services, the SRX4600 is optimized to provide consistent protection across private cloud environments.

Juniper Networks SRX firewalls
Juniper Networks SRX5400
The SRX5400 supports firewall performance of up to 480 Gbps, with advanced anti-threat capabilities and an unprecedented 42 million concurrent user sessions on a highly reliable system, with six-nines availability. It offers 10GbE, 40GbE, and 100GbE connectivity options for maximum flexibility.
Juniper Networks SRX firewalls
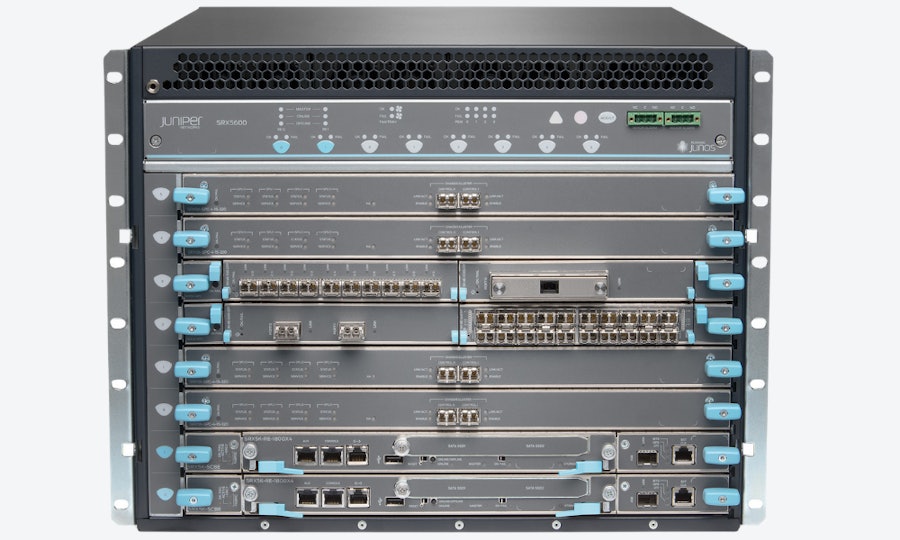
Juniper Networks SRX5600
Extraordinary scalability makes the SRX5600 Services Gateway particularly well suited for securing large enterprise data centers, service provider infrastructures, and next-generation services and applications, as well as enforcing unique per-zone security policies.
The SRX5600 supports firewall performance of up to 960 Gbps, advanced anti-threat capabilities, and an unprecedented 100 million concurrent user sessions on a highly reliable system, with six-nines availability.

Juniper Networks SRX firewalls
Juniper Networks SRX5800
Ideally suited for service providers, large enterprise, and public sector networks, the SRX5800 supports 2 Tbps firewall, six nines of carrier-grade reliability, more than 100 Gbps intrusion prevention system (IPS), and an industry record-breaking 100 million concurrent user sessions.

Juniper Networks SRX firewalls
Juniper Networks SRX1600
The SRX1600 provides high-performance connectivity, delivering up to 24 Gbps firewall throughput per unit with 25 Gbps interfaces and wire-speed MACsec for data security. With AI Predictive Threat Prevention, EVPN-VXLAN fabric integration, and a suite of security features managed by Juniper Security Director Cloud, the SRX1600 is a comprehensive solution for enterprise campus networks and small to midsize data centers.

Juniper Networks SRX firewalls
Juniper Networks SRX2300
The SRX2300 provides high-performance connectivity, delivering up to 35 Gbps firewall throughput per unit with 100 Gbps interfaces and wire-speed MACsec for data security. With AI Predictive Threat Prevention, EVPN-VXLAN fabric integration, and a suite of security features managed by Juniper Security Director Cloud, the SRX2300 is a comprehensive solution for small to midsized campus networks, data centers, and regional headquarters.

Juniper Networks SRX firewalls
Juniper Networks SRX4300
The SRX4300 delivers top connectivity, providing up to 90 Gbps firewall throughput and 100 Gbps interfaces, with wire-speed MACsec for security. Incorporating AI Predictive Threat Prevention and EVPN-VXLAN fabric integration, along with a full suite of security features managed by Juniper Security Director Cloud, the SRX4300 offers a comprehensive security solution for small to midsize campus networks, data centers, and regional headquarters.

Juniper Networks SRX firewalls
Juniper Networks SRX4700
The SRX4700 provides top-notch connectivity with up to 1.4 Tbps firewall throughput, 400 Gbps interfaces, and wire-speed MACsec for data security. Its integrated platform offers zero-trust capabilities, EVPN-VXLAN fabric integration, and AI Predictive Threat Prevention. Managed by Juniper Security Director Cloud, it delivers high-performance IPsec VPN, CGNAT, and unified policy management, catering to the needs of service providers, cloud providers, and large enterprises.
Ready to talk?
Are you looking for pricing details, technical information, support or a custom quote? Our team of experts in Basingstoke is ready to assist you.










